Configuration Options
This page provides a description of all configuration settings from left to right. The first four tabs are used to configure the backup client, the fifth is used to configure the backup service.
Schedule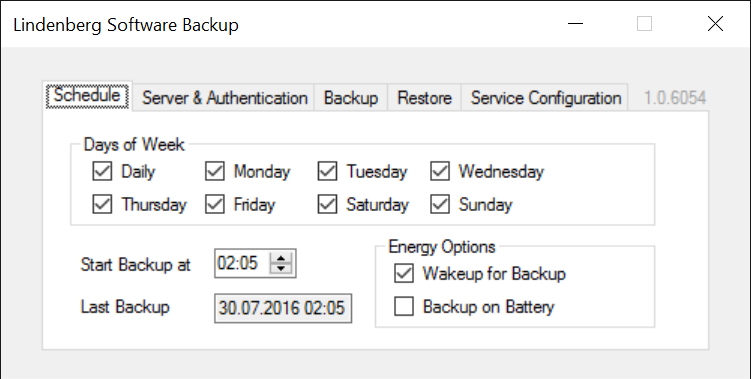
|
|
| Except for Last Backup all of these correspond to settings of the Task "Lindenberg Software Backup Background Task" that you can see in Task Scheduler | |
| Days of Week | on which days to run a backup |
| Start Backup at | allows to configure a convenient time to do backups |
| Last Backup | shows the last successful backup. As a backup can fail this is not the same as the last time a backup was attempted, and it always shows the time the backup was started, or more specifically, the shadow copies have been created. |
| Wakeup for Backup | whether the system shall wake up for a backup |
| Backup on Battery | whether to run a backup even on battery. Note that this may cause the backup to fail when running out of battery. If not turned on, the backup will be done when the system is plugged in again. |
Server & Authentication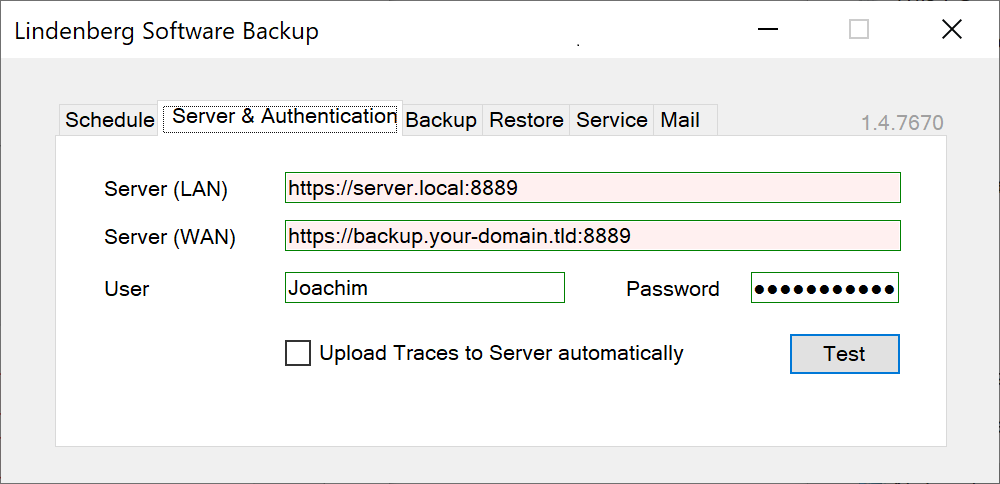
|
|
| Here you can configure the URLs to use, user and password for authentication, and Test connectivity. Note that changing any of the URLs will reset the password, as otherwise some other user might cause your password to be disclosed to a different server. Test will also check whether the certificates used are trusted or not, verify that both URLs point to the same server, and will remember info necessary to wake the backup server via Wake-On-Lan. See also Networking Aspects and Security Aspects. | |
| Server (LAN) | URL to connect to the server within your local area network. Usually the NetBIOS name of the computer running the backup service. This field is initially filled with a URL of a local service, just to show the format. |
| Server (WAN) | URL to connect to the server from outside of your local area network, including a fully qualified domain name |
| User & Password | User and password used for authentication to the (remote) backup service. User can also be a Microsoft account or a domain user. Users used for authentication should be different for different administrators/owners of computers. If owners/administrators overlap partially for different computers, you may want to use a different user per computer. This minimizes the risk of an administrator accessing files she is not supposed to access. See also Security Aspects. |
| Upload Traces to Server automatically | If enabled, traces will be zipped and sent to server in order to ease support for the administrator or development. Traces contain system and processing information, and may contain file or directory names. Traces never contain file contents. |
Backup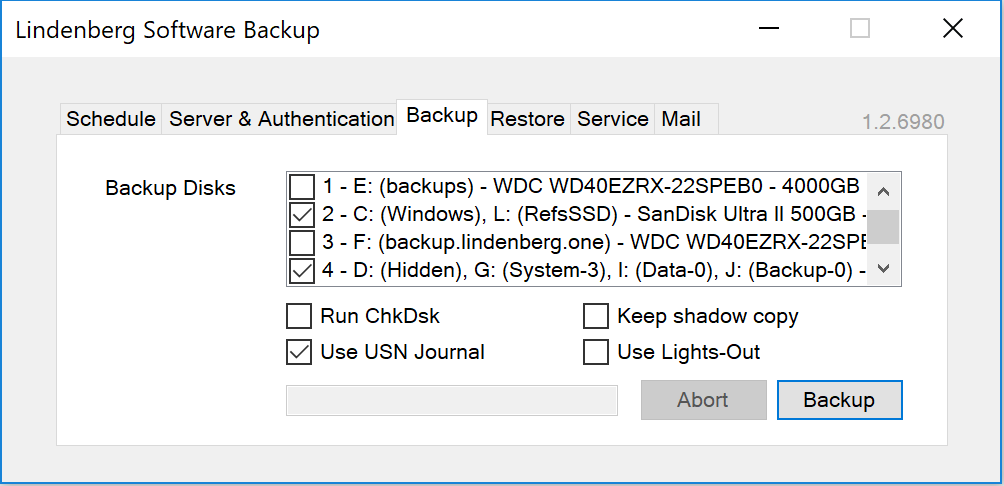
|
|
| Backup Disks | the disks to be backed up. Note that all disks are backed up in parallel. |
| Run Chkdsk | whether to run Chkdsk before a backup. This helps to identify issues with the source disks and report them to the user. Chkdsk may report transient issues, therefore this is only a warning. |
| Use USN Journal | Update Sequence Numbers (USN) are a mechanism to identify changes of files very fast. The primary use case is to identify modified documents that are to be processed by a file backup application. As Lindenberg Software Backup is a disk imaging backup application, it has to add additional logic to take advantage of the USN journal. In fact Lindenberg Software Backup implements two different variants of USN journal evaluation:
It is possible for applications to bypass the USN journal, and thus not all changes on a disk are necessarily reflected in the USN Journal. Because of this, Lindenberg Software Backup adds some monitoring - including running a journal verification run every 10th backup (picked at random) - to help identifying applications bypassing the journal and also potential issues in the algorithm used. If you receive Journal warnings or errors, then please send the traces to support@lindenberg.one for advice. Until then, you may prefer to turn off “Use USN Journal”. Also as a consequence of the extra processing required, there is no guarantee that using the USN journal is in fact faster then not using it. Whether it is faster depends on disk speed, number of files on your disk, rate of change, etc.. Typically the real disk storing your foto collection will benefit a lot more then the SSD that you boot from. When checking this feature, a dialog may show missing USN configurations for some volumes: 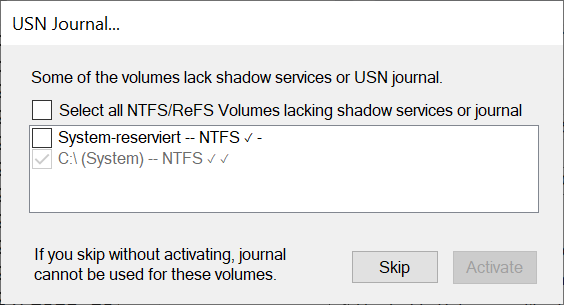 . .The recommendation is to select all NTFS volumes and activate the USN Journal there. |
| Keep shadow copy | whether to preserve the shadow copies created during backup in order to support Verification. Unless you want to do a verfication, turn the feature off, and then shadow copies created are deleted immediately after backup. |
| Use Lights-Out | whether to trigger a Lights-Out countdown after a backup. With Lights-Out 2.0 suspend will be triggered, with Lights-Out 1.x the final action will be triggered. Note that a countdown will only be triggered if the backup completes successful or with error, it is not triggered in case the backup is aborted by the user. See also Lights-Out 2.0 Integration. |
Restore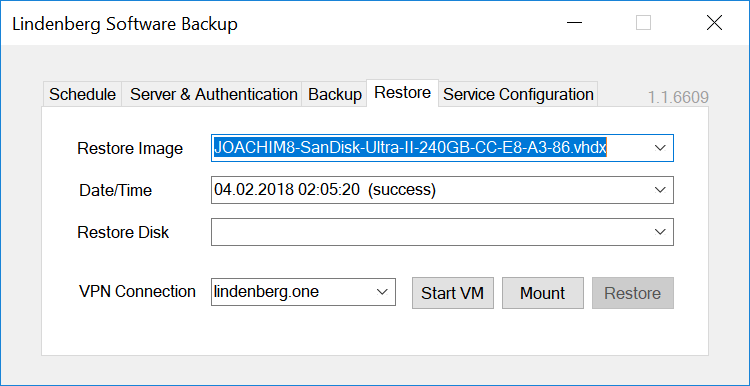
|
|
| See Restore Files and System, Verification & Validation. | |
| Restore Image | which of the images available on the server to restore. Note that the images shown depend on authorizations of the user you specified on the "Server & Authentication" Tab. |
| Date/Time | identifies which of the backups in the history to restore, and also whether the backup was successful or not. You should not restore backups that are not successful as they can be inconsistent. |
| Restore Disk | the disk to restore to. The disk must be at least as big as the original disk that was backed up. Warning: this disk will be erased during restore operation. |
| VPN Connection | If the server is not reachable, Backup will try to establish the selected VPN automatically. This setting is only shown if at least one appropriate VPN connection is configured. As the system needs to be able to access the mounted virtual disk, the VPN connection needs to be an "all users" connection (see how to create that with Windows 10, but think twice before saving credentials in the VPN connection if the system is used by other persons as well.) |
Service Configuration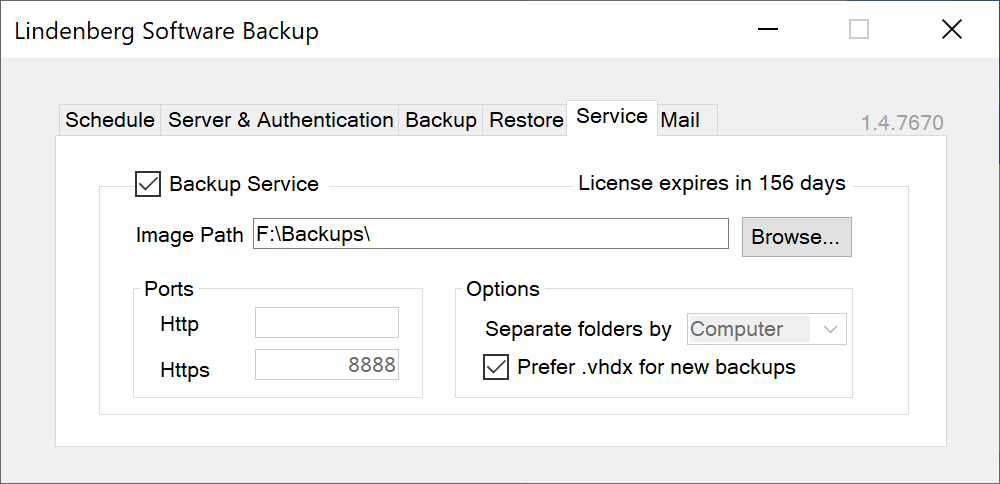
|
|
| Backup Service | whether to activate the backup service. On implies a service is created and started, with a specific service user, and the firewall is opened reflecting the http and https setting below. Because it would disrupt service to users and also because of the firewall configuration, the ports and separation mode cannot be changed while the service is active. |
| License expires... | tells you how long your license is still valid. If you click on that area, you can enter a new license code. Note that licesenes are validated regularly, and if you reuse the same license key on a different server, the license will be invalidated on the pervious server. |
| Image Path | defines the folder where to store the backups. Users that shall use backup service need to have at least read authorization on this folder and write authorizations to their respective subfolder.
|
| Ports | ports to use for communication. Http is supported only for debugging reasons, you should leave this field empty. If you want to do backups outside of your local area network you may have to open the https port in your firewall or configure port forwarding in your router. |
| Separate folders by -/User/Computer | this causes a subfolder to be created and used automatically for every user or computer respectively. Separate folders by User is equivalent to the "Enforce separate folders by user" in versions up to 1.3 and is the default for upgrades, whereas the default for new installations in version 1.4 and up is Computer. You can switch separation from User to Computer and Lindenberg Software Backup will move backups accordingly, but please contact support@lindenberg.one for instructions. The subfolder created will have full authorizations for SYSTEM, Administrators, the user triggering the backup, and the computer account in case you are in a domain. Other users that may have read authorizations on the folder set in Image Path above will not get any authorizations (unless they are member of the group Administrators). See Security Aspects for details. |
| Prefer .vhdx for new backups (1.1) | if set (recommended), backups will leverage the .vhdx format. See Backup Image Format for details. Note that Lindenberg Software Backup switches automatically to .vhdx if the disk size exceeds 2040GB or the disk uses a different sector size than 512 bytes. The only reason why you may want to use .vhd format is in case you want to be able to access files on a system or using software that does not support .vhdx format. |